To use a low-privileged accounts for ServiceControl instances, the following should be considered:
Access control on queues
The transport connection string used by ServiceControl must enable access to all of the ServiceControl queues as configured by the InstanceName setting:
- ServiceControl/InstanceName
- ServiceControl.Audit/InstanceName
- ServiceControl.Monitoring/InstanceName
The queues that ServiceControl needs to access will reflect the InstanceName used and the instance type:
If the connection string does not provide appropriate rights, the service may fail to start or may experience errors when certain operations are performed.
All instance types:
Both read and send permissions are required for each of these queues:
{InstanceName}:{InstanceName}.errors
Error instances:
{InstanceName}.: Both read and send permissions are required.staging error(see theServiceBus/setting): Read permission is required.ErrorQueue error.(optional, see thelog ServiceBus/setting): Send permission is required.ErrorLogQueue - The Error instance will require send permission for every endpoint queue to allow for failed message retries.
- If subscribing to ServiceControl integration events, send/publish permission to the subscriber queues and/or any pub/sub mechanism for the transport will be required.
Audit instances:
audit(see theServiceBus/setting): Read permission is required.AuditQueue audit.(optional, see thelog ServiceBus/setting): Send permission is required.AuditLogQueue
For MSMQ, the ACL default for a queue allows Administrators full access. Switching to a low-privileged account requires modification of rights to give full control to the custom account.
Filesystem paths
The service account running ServiceControl instance requires following filesystem level access rights:
| Path | Rights |
|---|---|
Executables (e.g. C:\) | Read |
Logs (e.g. C:\) | Write |
Database (e.g C:\) | Write |
Database volume (e.g. C:) | Read Attributes |
The database volume Read attributes access right is needed by ServiceControl to query for total and total free space on the volume.
Performance counters
ServiceControl requires access to Windows performance counter infrastructure. As a result the service account needs to be a member of Performance Monitor Users group.
Testing the configuration
These methods confirm that the service account has sufficient rights:
- Configure the ServiceControl Windows service to run under the custom service account, start it and check the log files.
- Interactively run ServiceControl under the custom service account.
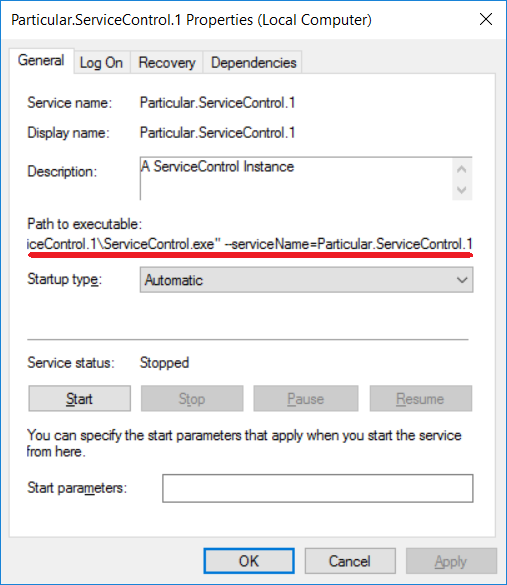
When running ServiceControl. from the command line, it is important to use the same command line switches that are used when running the Windows service. The command line is visible from within the standard Windows Services user interface.
Method 1: Running the service as a non-privileged user
- Open Computer Management.
- Change the service account to the custom user, provide the password and apply the change. The account will be given "logon as a service" privilege.
- Start the service and confirm that it started.
- Examine the log file to ensure that the service is operating as expected. If the service does not start and the log file does not indicate the issue, try Method 2.
Method 2: Running the service interactively as a non-privileged user
To run the service this way, the custom service account must have rights to log on interactively on the computer.
- Log on to the computer with admin privileges.
- Switch to the appropriate domain and username.
- Issue the following command, entering the password when prompted:
For example
runas /user:MyDomain\MyTestUser cmd.exe
If the command returns the error below, then the user account cannot be tested this way without adjusting the login rights. Normally this only occurs if the computer is configured as a domain controller or the system administrator has restricted login access using group policies.
1385: Logon failure: the user has not been granted the requested logon type at this computer.
Once login rights are granted:
- Ensure that the service is stopped.
- From the command prompt running as the service account, change to the ServiceControl installation directory and run
ServiceControl.with theexe --serviceNameparameter. In the following example, the default name has been used. Check ServiceControl Management if unsure of the service name - Examine the output and confirm that there are no critical errors.
- Shut down the console session.
- Start the service.
ServiceControl.exe --serviceName=Particular.ServiceControl
Specify the correct name of the service on the command line as this impacts the queue names used.